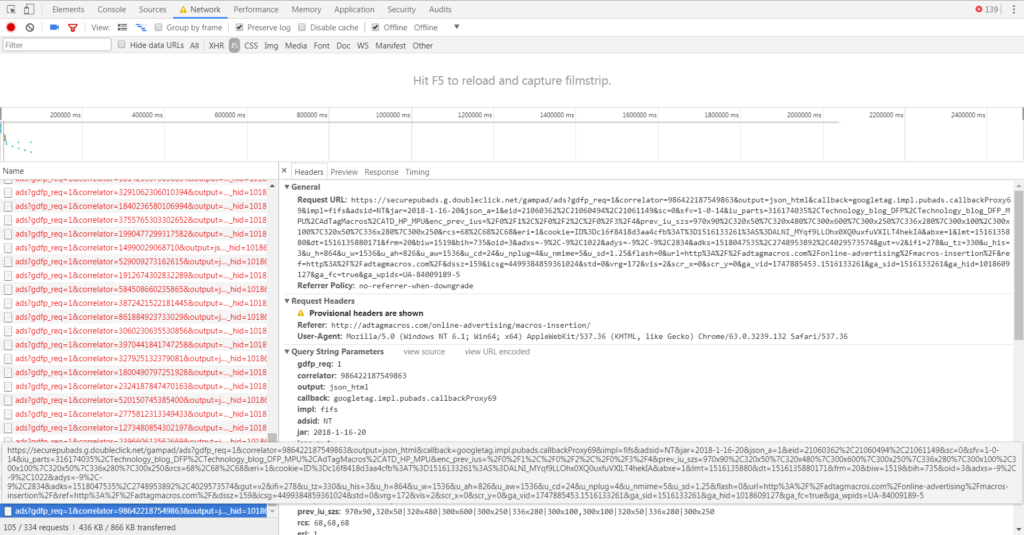
A few days back, while checking the issue raised by the publisher, We have observed that when Google Ads load on the page, Certain script get loaded which increased the CPU usage exponentially.
On further Investigation, We have come across Script from coinhive domain which is running at the backend and serving as mining script.
Most Of the antivirus highlighted this issue and blocked it immediately.
After Few days, the News have been confirmed by the trendmicro,IT security company, You can read full article Malvertising Campaign Abuses Google’s DoubleClick to Deliver Cryptocurrency Miners
Before diving deep into the details, Let’s check few details about mining.
What is Cryptocurrency mining?
mining is the process by which transactions are verified and added to the public ledger, known as the blockchain, and also the means through which new Cryptocurrency (bitcoins) are released. Anyone with access to the internet and suitable hardware can participate in mining. The mining process involves compiling recent transactions into blocks and trying to solve a computationally difficult puzzle. The participant who first solves the puzzle gets to place the next block on the blockchain and claim the rewards. The rewards, which incentivize mining, are both the transaction fees associated with the transactions compiled in the block as well as newly released bitcoin.
Read more: Bitcoin Mining
Why it matters to us ?
In Initial days, It was just related to the users who want to start mining. Which means they will utilize their own HardWare resources to perform the mining. But Hackers now developed few script which can actually utilize normal user CPU to perform mining operations.
Coinhive provides a way to mine a cryptocurrency known as Monero. Monero differs from other cryptocurrencies like Bitcoin, in that it does not give miners who use GPUs or other specialized hardware a significant computational advantage. That means it is well-suited to use in web browsers, executing as JavaScript on consumer CPUs.
Site owners who place the Coinhive code on their websites earn Monero currency. The Coinhive code uses site visitors’ computational resources to mine Monero. An attacker can place the Coinhive code on thousands of websites and earn Monero from the mining that happens in site visitors’ browsers.
Coinhive Attack on the Advertising Industry
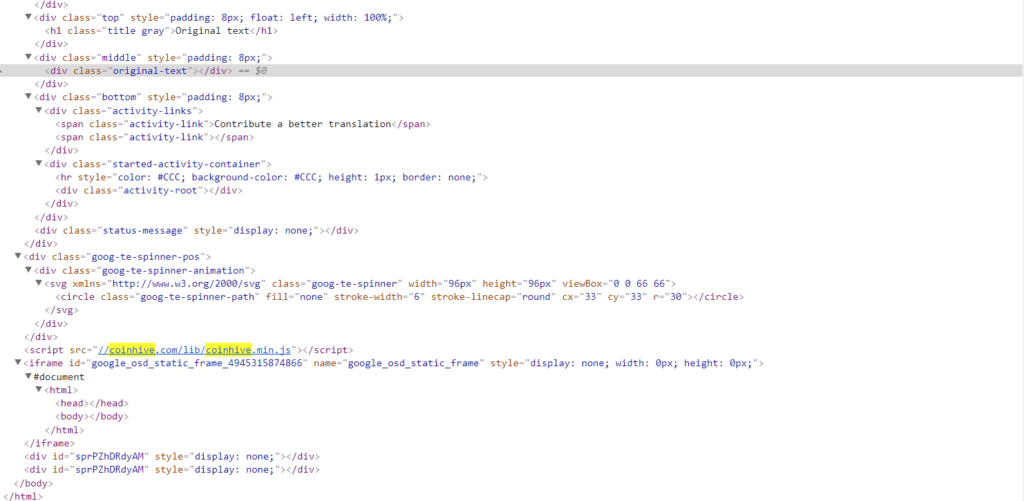
When I first came across this issue, To investigate it further, I have turned off my internet and check the source code, The Infected coin miner script is loading from the coinhive domain site. And it is being loaded with the google Iframe.
Online tools to check whether site you are visiting is running any mining script or not.
http://whoismining.com/
virusTotal
How To Remove the JS.MINER script From Your System
Symantec Coinhive remover
https://www.symantec.com/security_response/writeup.jsp?docid=2015-092321-2230-99
Steps To Protect From Getting your site Or system Infected
1) Always login from the Trusted System if you are managing your own site
2) Keep your Antivirus Updated
3) At least install malwarebytes
4) Keep your browser safe by downloading the plugins from trusted source
5) Install No-Coin Plugin To secure your browser